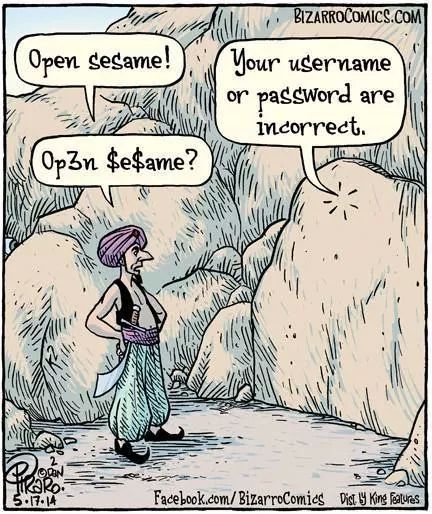
There is no greater threat than the assassin’s bullet. It is the slayer of kings. It cares not about your legacy or fortune. It is the great equalizer. It can change the destiny of men and countries. In information technology speech, the assassin’s bullet is a perfect metaphor for your administrator passwords. Your login and password security can be the gateway to riches, ruin, or embarrassment for your organization. Unfortunately, too many CEOs do not fear it as much as they should.
After working with hundreds of companies, we have noticed that the holy grail of the administrator password is often more vulnerable than it should be.
Well Banjo, looks like you’re Cujo now… but don’t get attached to it.
First, even complex passwords are often a known derivative of vendors or network admins themselves. A recent analysis of passwords by Lorrie Faith Cranor found that people tend to use the same symbols, something that is very easy to type, a common pattern, or things that remind them of what they’ve created the password for. Or they create their password based on things that make them happy. While these tricks make their passwords easier to remember, it also makes them much easier to hack . We have also found that admins rarely (if ever) change their administrative password and that password management on routers, switches, and peripherals is nonexistent. As security expert Bruce Scheiner pointed out in a recent blog, “If the director of the CIA can’t even keep his e-mail secure, what hope do the rest of us have — for our e-mail or any of our digital information?” Now, CIA Director John Brenner should know better than to construct a weak password, right?
Well, apparently his password wasn’t really hacked. Brennan was Doxed.
What is Doxing? Short for documenting, it involves researching and using someone else’s personal information. In Brennan’s case, a hacker pretended to be a Verizon employee to steal data about Brennan’s Verizon account, including his personal AOL address and bank card information, and then used it to have AOL reset his password.
So, what is the answer to this password security riddle?
Could someone pose as one of your network admins - or you - and obtain critical information to gain access to confidential information? No one deserves being the target of these sorts of attacks where personal or corporate information could be compromised and/or leaked to the public. So how do you defend against them ?
As Schenier so eloquently stated, “It’s only when the costs of insecurity exceed the costs of doing it right that companies will invest properly in our security.”
My job as a strategic consultant is not easy. How do you convince CEOs and CIOs to question their current policies and procedures and make them understand all of the factors involved with data and password security?
What we suggest is starting with a strategic risk assessment to provide you with a clearly defined road-map that independently assesses risk, urgency, costs and liabilities, which define a vision and provide a lattice work to base your corporate well-being and security around.
Next - what is this “strategic road-map”?